The OSI Model | Fundamentals
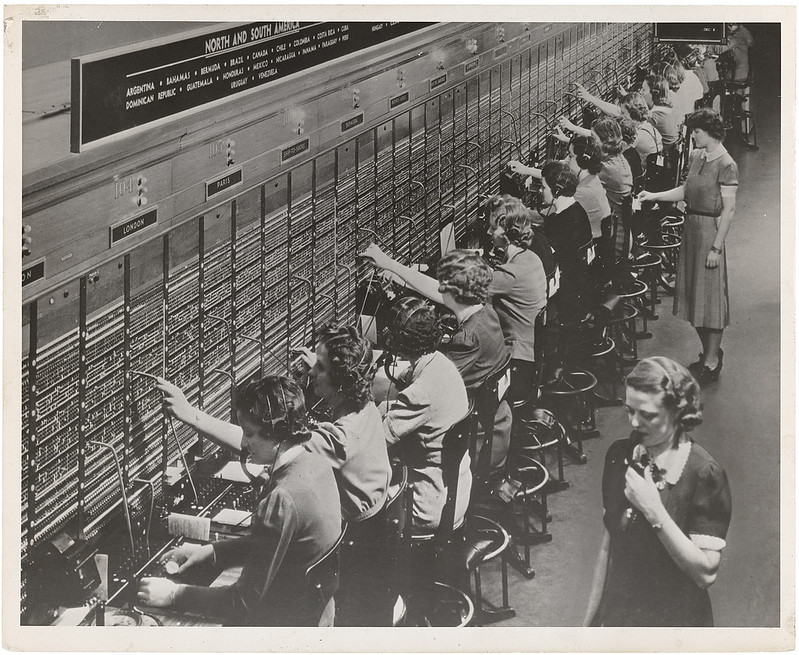
When you encounter complex technologies, you need to simplify the process by breaking it down into simple, isolated processes and actions. This is done by using a network model. Practice is important but without a guideline/roadmap you might get stuck or come up with a solution that is not the most optimal one.
(more…)