In my last post, we explored the fourth layer of the OSI framework: the transport layer. As we saw, this layer is responsible for a transparent data flow between end systems and/or hosts. It is also responsible for the recovery of errors between end-to-end data transfers and flow control, and layer 4 ensures that data transfer is complete.
In this post, we move to the fifth layer of the model. This layer is the “Session” layer and establishes, manages, and terminates connections between applications. Essential is the verification that the user using the application is also the user that is allowed to use the application.
Sessions
The session layer’s first and most important responsibility is creating a session. Let’s take this as an example. You have a device and want to communicate with a server and connect with the server, and you have to start a session. You can see how a session works below (very simplified):
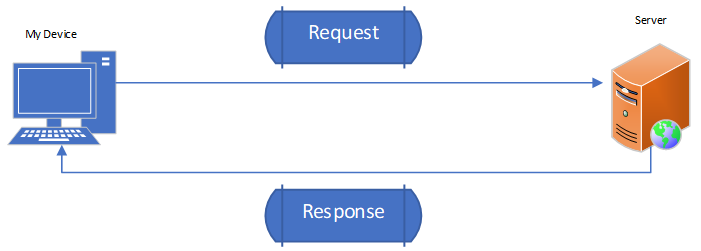
By trying to connect to the online server with your desktop, laptop, or mobile, you send a request from your device to the online server. With this request, the first responsibility of a session comes into play: authentication.
Authentication
With authentication, you verify that whoever is trying to access the application is also that person that wants to access that application. Authentication is the combination between a username and a password: the most classic form, but there are other ways to authenticate like a security token such as a smart card, fingerprint, or a digital certificate. It can also be a combination of all these possibilities of authentication. After the application checks and validates your identity, the server sends back a response to your device. This response is the permission to create a session with the application. By permitting you, the server authorizes you to use the application.
Authorization
Authorization is a set of privileges that defines what an authenticated person can do in the application. Different operating systems and applications provide various schemes for authorization. For instance, a classic Windows scheme is to assign permissions to a specific user account. Authorization is a critical part of network hardening techniques and helps you define how to set user access levels for an operating system or an application. Different users of an application might have other rights.
If you want to study a language, you can use the app “Duolingo.” Duolingo is free to use, but there is also a possibility to get many more features. For these features, you have to pay. So, when a user pays, this user has different rights (privileges) on the Duolingo server than a person that uses the free version: different users with other rights.
Accounting
Accounting is responsible for monitoring the resources users consume when they have network access. You can monitor, for example, system time, the amount of data that is sent and received during a session, and bandwidth. Servers monitor logged-in users with the support of an event log.
AAA Standards
Two basic standards are available to secure the AAA (Authentication, Authorization, and Accounting) standards. These two standards are RADIUS and TACACS+.
RADIUS
RADIUS stands for Remote Authentication Dial-In User Service and is the most popular of the two AAA standards. Network techs created RADIUS to support Internet Service Providers (ISPs) with thousands of modems in tons of computers to connect to a single central database. Network techs originally designed RADIUS for dial-up connections, but RADIUS evolved into a solution for all types of wired and wireless networks.
RADIUS has three components: (1) the RADIUS server that has access to a database of usernames and passwords, (2) several network access servers (NASs) that control the modems or wireless access points, and (3) a group of systems that connect to a network in some way. If you want to use RADIUS, you require a RADIUS server. A single RADIUS server can provide multiple NASs and a complete Point to Point Protocol (PPP) connection from a requesting system through the NAS to the RADIUS server. The RADIUS server, like all PPP connections, supports PAP, CHAP, and MS-CHAP. RADIUS performs authentication on UDP port 1812 or UDP port 1645 and uses UDP ports 1813 and 1646 for accounting.
TACACS+
Routers and switches require administration. If you have a simple network, you can access an administration screen for each router and switch by simply entering a username and a password for every device. If your network becomes more complex with many routers and switches, it becomes near impossible to log into every device separately. You can make a single server store the Access Control List (ACL) for all the devices in your network to solve this problem.
You do this with the Terminal Access Controller Access Control System Plus (TACACS+). TACACS+ is a protocol developed by Cisco and supports AAA in a network with many routers and switches. It is very similar to RADIUS but uses TCP port 49 by default. In addition, it separates authorizations, authentication, and accounting into different parts and uses PAP, CHAP, and MD5 hashes. TACACS+ can also use Kerberos as part of the authentication scheme.
Kerberos
Kerberos is an authentication protocol for TCP/IP networks in which many clients are all connected to a single authentication server. Kerberos has no connection to PPP and works excellent in a network. Microsoft has adopted Kerberos for all Windows networks by using a domain controller. The Windows domain controller stores a list with all usernames and password hashes in Active Directory. If you log onto a computer that is a member of a Windows domain, the hash of your username and password goes directly to the domain controller. This domain controller uses Kerberos for authentication.
Session Restoration
Another vital part of a session is the possibility of restoring a session. You can also call this “checkpointing.” If you open a lot of tabs in your browser and your system shuts down because of whatever reason, you have the option to restore your sessions once you return to your browser. You can again open the tabs you opened at an earlier point by clicking on the restoration option. You open all your tabs again by clicking on the restoration option, restoring all your previous sessions. The session layer saves the time you use the system and the states and values during that session. By saving the session, you prevent the risk of data loss. Sometimes, immediate session restoration at a point where you stopped is not handy. For instance, when you use a bank application. For security reasons, the session is fully closed without any option to start at the point where you stopped. You have to log into the session again and start at the beginning. You do this to prevent third parties from hijacking your session, creating a serious security risk. Within the session layer, you can define what sessions must be restored and discarded in specific applications.
When downloading big chunks of data, you use restoration by a method called “checkpointing.” Checkpointing builds specific thresholds into a session to which you immediately return when disconnected, and this saves that hassle of starting all over again. Let’s say you are downloading a game of 500MB, and the application has built up the session into the below checkpoints (CPs):
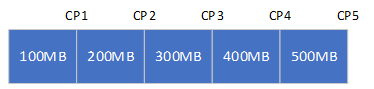
When you disconnect at 275MB, you automatically restart at the latest checkpoint you passed: 200MB, which is CP1.
Flow Control and Synchronization
In case you are in a webinar, an online meeting, or watching a streaming video, it is essential to secure Synchronization. Synchronization means that audio and video play simultaneously: when something is said (audio), you must capture the image at the right moment (video). It would help if you precisely captured what you said simultaneously. Otherwise, dialogues are going forward and backward, which can create a lot of confusion. Imagine that you see someone banging on a door. You only hear the banging after the image disappears during another shot when the movie’s character is talking. That isn’t very pleasant. The session layer takes care of this: it is responsible that sound and video are captured and played at the same time in a synchronized way. It is responsible for flow control and Synchronization.
Final Thoughts
Layer 5 establishes, manages, and terminates the connections between applications. It also sets up, coordinates, and terminates conversations, exchanges, and dialogues between the different applications at each end. It deals with session and connection coordination.
There is one crucial point about layer 5. Unlike all the other layers, the session layer is not provided/serviced by the Operating System and its kernel (the core that provides essential services for all other parts of an Operating System). Developers don’t code in the Operating System or its kernel; developers do this within your application. All options discussed (authentication, authorization, accounting, session restoration, and flow control/synchronization) should be coded inside the app regardless of whether you use a mobile or web app. In other words: it’s the application layer’s responsibility, which I will also discuss in one of my next posts.
Feel free to contact me if you have questions or in case you have any additional advice/tips about this subject. If you want to keep in the loop if I upload a new post, do not forget to subscribe to receive a notification by email.